Proxy vs VPN: Key Differences Most People Miss
The debate around Proxy vs VPN is usually framed as a simple privacy question. One hides your IP, the other encrypts your traffic. That explanation is not wrong, but it’s incomplete in ways that matter in real-world use.
For developers, marketers, network engineers, and even everyday users trying to access restricted services, the practical differences between proxies and VPNs go far beyond surface-level definitions. They affect detection, performance, trust, cost, and how reliably your traffic behaves under scrutiny.
This article looks past the usual marketing narratives and examines how proxies and VPNs actually work on live networks, how websites interpret them, and where each one genuinely fits.
How Proxies Actually Work in Practice
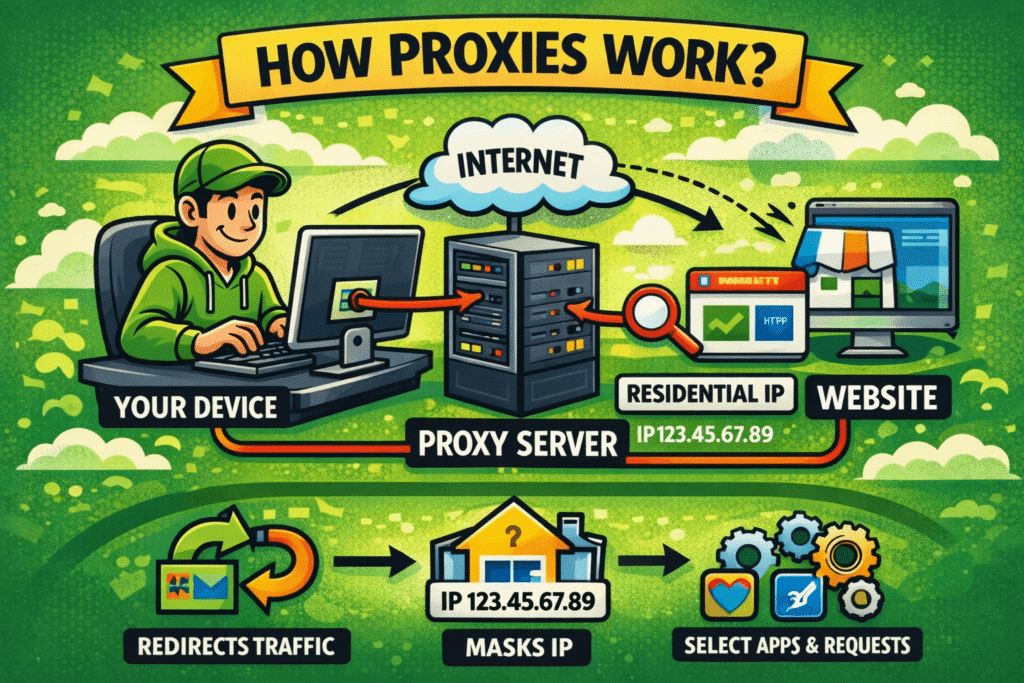
A proxy server acts as an intermediary between your application and the destination server. Instead of connecting directly, your request is forwarded through a proxy IP, and the response comes back the same way.
What often gets overlooked is scope. A proxy usually operates at the application level. Your browser, script, or tool is explicitly configured to use it. Other system traffic remains untouched.
In real usage, this means proxies are precise tools. A scraper can use one proxy pool, a browser another, and your system traffic none at all. That granularity is why proxies dominate automation, testing, and data collection workflows.
Proxies also come in many forms—datacenter, residential, mobile—and support different protocols like HTTP, HTTPS, and SOCKS5. Each choice changes how your traffic looks to the outside world. Some forward headers transparently, others rewrite them. Some rotate IPs per request, others hold sessions steady.
The key point: a proxy doesn’t try to hide everything. It redirects traffic in a controlled, deliberate way.
How VPNs Behave Beyond the Basics
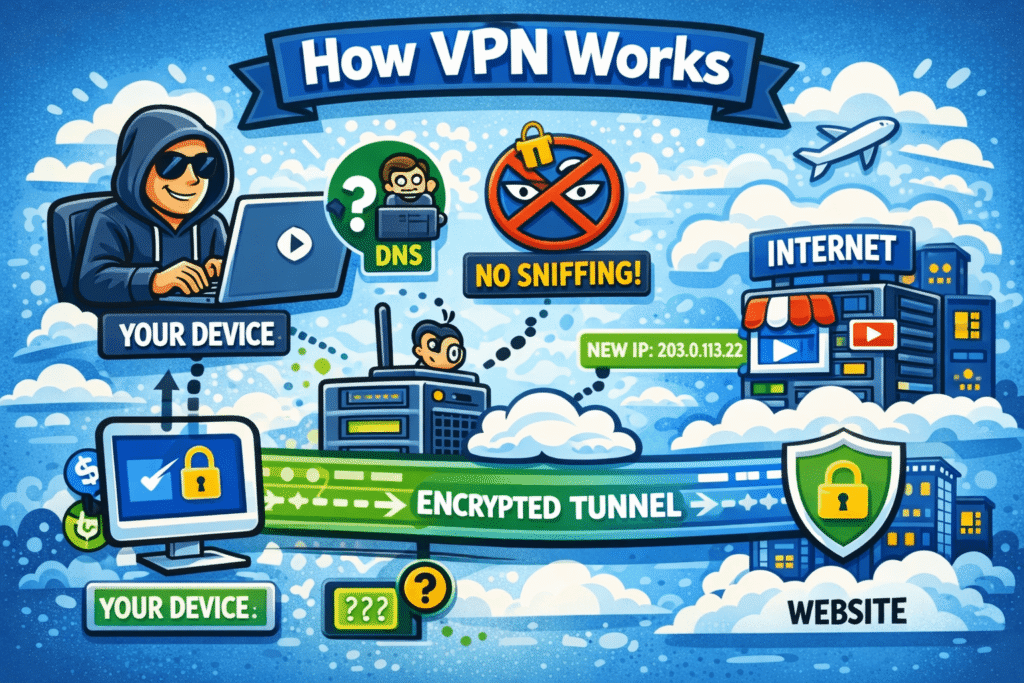
A VPN works at a lower level of the network stack. Once connected, it creates an encrypted tunnel between your device and the VPN server, routing all traffic through that tunnel by default.
From the outside, your device appears to be the VPN server. From the inside, your operating system treats the VPN as a new network interface.
This design makes VPNs excellent for securing traffic on untrusted networks, such as public Wi-Fi, and for general-purpose privacy. Encryption is always on, DNS is often handled by the VPN provider, and apps don’t need individual configuration.
However, this “all-or-nothing” behavior is also a limitation. You can’t easily route one app through a VPN and another outside without split tunneling, which adds complexity and potential leaks.
VPNs are built for users, not workflows. They prioritize simplicity and blanket coverage over fine-grained control.
Proxy vs VPN: Traffic Visibility and Encryption
One of the most misunderstood aspects of Proxy vs VPN is encryption.
A VPN encrypts traffic between your device and the VPN server. This protects data from local network observers and ISPs. However, once traffic exits the VPN server, it behaves like any normal connection to the destination site.
A proxy, on the other hand, may or may not encrypt traffic. HTTPS proxies encrypt browser-to-proxy communication via TLS, but the proxy still sees your requests in plaintext internally. SOCKS5 proxies can pass encrypted traffic if the application itself uses TLS, but the proxy does not add encryption on its own.
This distinction matters less for websites—modern HTTPS already encrypts end-to-end—but more for trust. With a VPN, you trust one provider with all your traffic. With a proxy, you trust it only with the specific connections you send through it.
Detection: Why Websites Treat Them Differently
Detection is where the proxy vs VPN conversation becomes genuinely practical.
VPN IP ranges are widely known and heavily reused. Large consumer VPN providers concentrate thousands of users behind limited IP pools. As a result, many websites can identify VPN traffic using IP reputation alone.
Proxies, especially residential and mobile ones, blend into normal consumer traffic far more effectively. A residential proxy uses IPs assigned to real household connections, which look identical to ordinary users at the network level.
Behavior also plays a role. VPN users tend to generate mixed traffic patterns—streaming, browsing, downloads—from shared IPs. Proxy traffic is often task-specific and can be tuned to mimic realistic usage.
This is why VPNs are frequently blocked outright, while proxies are selectively filtered based on behavior, headers, and session consistency.
Trust Models and Risk Exposure
Trust is rarely discussed honestly in marketing comparisons.
When you use a VPN, you centralize trust. Every application, every protocol, every connection passes through one provider. If logging exists, misconfiguration happens, or legal pressure is applied, the entire traffic profile is exposed.
Proxies distribute trust. You might use one provider for scraping, another for browsing, and none for personal accounts. Exposure is segmented by design.
That doesn’t make proxies inherently safer. Low-quality proxy providers can inject headers, log aggressively, or resell traffic. The difference is that proxies allow selective risk, while VPNs bundle all risk into a single tunnel.
For professionals, that distinction is critical.
Performance and Latency in Real Use
VPN performance is shaped by encryption overhead and tunnel routing. While modern protocols are efficient, encryption still adds CPU cost, and traffic often takes longer paths through centralized servers.
Proxies usually introduce less overhead. There’s no tunnel negotiation, and traffic can be routed closer to the destination. For latency-sensitive tasks—API calls, scraping, automation—proxies are often faster and more predictable.
That said, consumer VPNs are optimized for streaming and browsing, not high request concurrency. Proxies are built for scale, but only if the provider’s infrastructure can support it.
Performance isn’t about “proxy vs VPN” in isolation. It’s about whether the tool matches the workload.
Cost Structures Most People Ignore
VPN pricing is simple: a flat monthly fee for unlimited or high-volume usage. This works well for individuals but poorly for businesses with specialized needs.
Proxies are priced by IP count, bandwidth, or request volume. This makes them more expensive upfront but more transparent. You pay for exactly what you consume.
For large-scale operations, proxies can actually be cheaper because traffic is targeted. For casual users, VPNs feel more economical because the cost is predictable.
The mistake is assuming one pricing model fits all use cases.
A Short, Practical Comparison
At a high level, the Proxy vs VPN decision comes down to intent:
- If you need system-wide privacy and encrypted traffic on untrusted networks, a VPN is the right tool.
- If you need control, scalability, and realistic IP behavior for specific applications, proxies are the better fit.
Neither replaces the other. They solve different network problems.
The Verdict: Experience Over Labels
The real takeaway from the proxy vs VPN discussion is that neither is “better” in a universal sense. They reflect different design philosophies.
VPNs are built for simplicity and broad protection. Proxies are built for precision and adaptability.
People run into trouble when they use VPNs for tasks that require identity realism, or proxies for tasks that require blanket security. Understanding how traffic actually flows—and how it’s judged by modern systems—matters more than the name of the tool.
If you choose based on behavior, not branding, the decision usually becomes obvious.