Using Proxies for Social Media Management: Pros and Risks
Managing social media at scale has quietly become a networking problem as much as a marketing one. Whether you’re handling multiple brand accounts, running regional pages, or supporting client portfolios, platforms increasingly expect predictable, human-like behavior from a limited set of locations and devices. That expectation collides with the realities of modern workflows, where teams log in from different places, automation tools perform repetitive actions, and accounts are accessed far more frequently than a single person ever would.
This is where using proxies for social media management enters the conversation. Proxies are often discussed as a workaround or a growth hack, but in practice they sit at the intersection of operational stability, risk management, and platform compliance. Used carefully, they can reduce friction and account lockouts. Used poorly, they can accelerate bans and undermine trust. Understanding both sides matters more than ever.
Why Proxies Matter in Social Media Operations
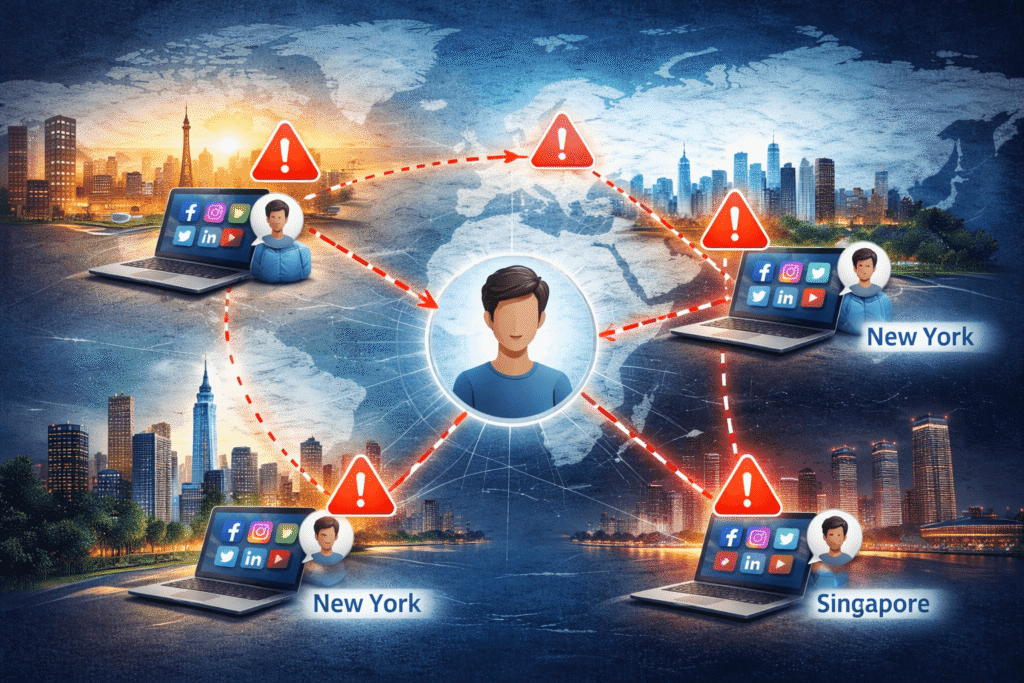
Social platforms rely heavily on IP addresses to establish behavioral context. An account that logs in from Berlin in the morning, New York in the afternoon, and Singapore at night triggers obvious red flags. Even when credentials are valid, inconsistent network signals are treated as potential account compromise or automated abuse.
For teams managing multiple accounts, this creates structural pressure. Logging everything from one office IP can look unnatural at scale. Distributing access across home connections, VPNs, or cloud servers introduces its own inconsistencies. Proxies emerged as a way to stabilize the network layer so that account behavior aligns more closely with how real users appear to platforms.
The key is that proxies don’t change what you do on social media. They change how your activity is perceived at the network level. That distinction drives both their benefits and their risks.
How Proxies Are Used in Social Media Management
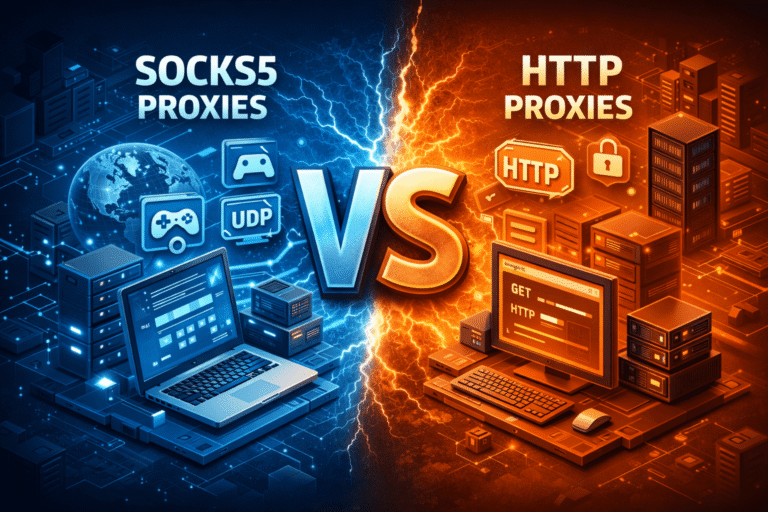
At a technical level, a proxy acts as an intermediary between your device or tool and the social platform. Requests are forwarded through another IP address, masking your original connection. In social media workflows, this is typically done in three scenarios.
First, account separation. Each social account is assigned a consistent IP profile, reducing overlap and cross-account linkage. Second, geographic alignment. Accounts intended to represent a specific country or city appear to originate from that region. Third, tool integration. Scheduling and analytics platforms often centralize activity through servers that would otherwise look suspicious without IP diversification.
In real-world use, proxies are rarely a standalone solution. They are combined with browser profiles, device fingerprints, session persistence, and conservative activity pacing. When any one of these elements is ignored, the proxy itself becomes a liability rather than a safeguard.
The Practical Benefits of Using Proxies for Social Media Management
The strongest argument for proxies is not growth or automation. It’s operational consistency.
From a detection standpoint, stable IP usage reduces the likelihood of forced logouts, security checkpoints, and sudden verification requests. Platforms expect accounts to behave predictably over time, and proxies can help maintain that predictability when multiple people or systems are involved.
From a trust perspective, proxies can prevent accidental association between unrelated accounts. Without them, platforms may infer that several brand pages belong to the same operator simply because they share an IP history. This can be especially problematic when one account experiences a violation that spills over to others.
Performance also plays a role, though it’s often misunderstood. High-quality proxies can provide low latency and reliable connections, particularly when accessing region-specific endpoints. Poor proxies, on the other hand, introduce delays, failed requests, and inconsistent session handling that actively harm account health.
Cost is the final benefit, but only in context. Compared to the time lost resolving bans, recovering accounts, or recreating assets, a well-chosen proxy setup is often cheaper in the long run. That said, low-cost proxies tend to externalize their costs through higher risk, which brings us to the downside.
The Risks and Limitations You Can’t Ignore
The most common mistake in social media proxy usage is assuming that any proxy is better than none. In reality, proxy quality matters more than proxy presence.
Detection systems are sophisticated enough to recognize entire IP ranges associated with abuse. Datacenter proxies, especially shared ones, are often flagged long before you ever log in. Using them for account access can increase scrutiny rather than reduce it.
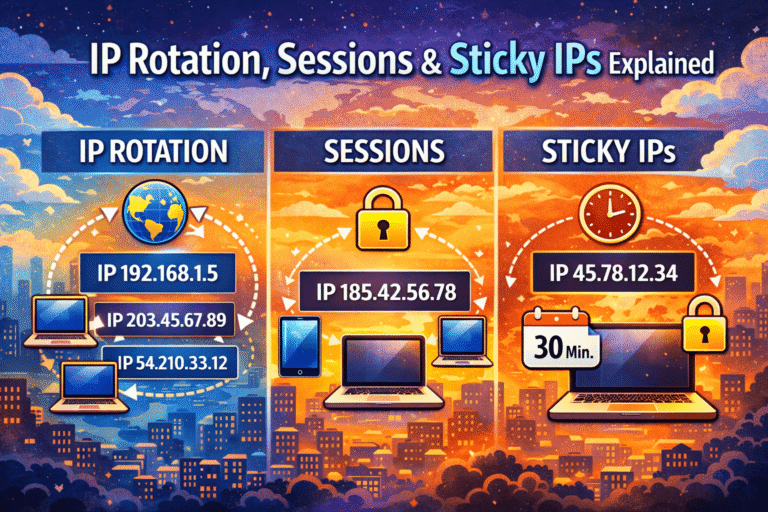
Trust issues extend beyond the platform. Some proxy providers log traffic, reuse IPs aggressively, or rotate addresses without warning. This breaks session continuity and can trigger security alerts even if your behavior is otherwise clean.
There’s also a performance trade-off. Overloaded or geographically mismatched proxies introduce latency that causes partial page loads, failed uploads, or API errors. These anomalies don’t just frustrate users; they generate abnormal interaction patterns that platforms monitor.
Finally, cost can escalate quickly. Residential or mobile proxies suitable for social media are significantly more expensive than generic alternatives. When teams scale without a clear IP strategy, proxy expenses can grow faster than the value they protect.
Detection, Trust, and Platform Behavior
Social platforms don’t ban proxies outright. They ban patterns.
An account accessed from a single, stable residential IP with human-like timing is often indistinguishable from a normal user. The same account accessed from a rotating pool of known proxy IPs, logging in repeatedly, changing locations, and performing scripted actions stands out immediately.
Trust is built over time. Proxies should support that process, not disrupt it. Sticky sessions, consistent geolocation, and long IP lifetimes align better with how platforms model legitimate users. Aggressive rotation, frequent IP changes, and mismatched regions undermine that trust, even if the proxy itself is technically “clean.”
A Short, Practical Comparison
In practice, social media teams gravitate toward three broad proxy approaches. Residential proxies offer the highest trust but require careful management and higher budgets. Datacenter proxies are affordable and fast but carry elevated detection risk. Mobile proxies provide excellent legitimacy but are often cost-prohibitive for large operations.
The right choice depends less on the proxy type and more on how closely it matches your account behavior, geographic intent, and scale.
Performance and Cost in Real Operations
Performance is rarely about raw speed. It’s about reliability. A slightly slower but consistent connection is preferable to a fast one that drops sessions or rotates IPs unpredictably.
Cost should be evaluated per protected account, not per gigabyte or IP. If a proxy setup reduces account churn, lowers manual intervention, and minimizes recovery efforts, it often pays for itself. When it doesn’t, the issue is usually misconfiguration or a mismatch between proxy type and use case.
Verdict: A Tool, Not a Shortcut
Using proxies for social media management is neither inherently good nor inherently risky. It’s a structural response to how platforms interpret network signals at scale.
In experienced hands, proxies stabilize access, reduce false positives, and support legitimate multi-account workflows. In careless setups, they amplify detection, erode trust, and create more problems than they solve.
The practical takeaway is simple: proxies should make your activity look more like a real user, not less. When they do, they become a quiet but valuable part of modern social media infrastructure. When they don’t, no amount of technical sophistication will compensate.